Technology
123safe67: The Digital Fortress for Your Personal Data in an Era of Cyber Threats

Introduction to123safe67
In today’s digital landscape, our personal data is more vulnerable than ever. Every click, every transaction, and every interaction online carries the risk of falling into the wrong hands. As cyber threats become increasingly sophisticated, protecting your sensitive information has never been more critical. Enter 123safe67—a powerful solution designed to fortify your digital presence against a tide of cyber attacks.
Imagine having a virtual fortress that safeguards your personal data while allowing you to navigate the internet with confidence. With 123safe67 by your side, you’ll not only shield yourself from relentless hackers but also enjoy peace of mind in an age where privacy feels like a luxury. Let’s dive deeper into how this innovative platform can be your ultimate guardian in a world fraught with digital dangers.
The Growing Threat of Cyber Attacks
Cyber attacks are no longer just the stuff of movies. They have become a daily reality for individuals and businesses alike. The rise in digital connectivity has opened up countless doors, but it has also created vulnerabilities.
Hackers are constantly evolving. Their tactics range from phishing scams to sophisticated ransomware attacks that can cripple entire organizations overnight. Every click on a dubious link or download of an unverified file increases the risk of falling victim to these threats.
Data breaches occur with alarming frequency, exposing personal information at unprecedented levels. Even major corporations aren’t immune; high-profile incidents dominate news headlines, leaving consumers feeling anxious about their own security.
As our reliance on technology grows, so does our exposure to potential breaches. It’s crucial now more than ever to prioritize digital safety and seek robust solutions like 123safe67 before it’s too late.
How 123safe67 Can Protect Your Personal Data?
123safe67 employs advanced encryption technology to safeguard your personal data. This means that sensitive information is transformed into a secure format, making it unreadable to unauthorized users.
Moreover, 123safe67 utilizes multi-factor authentication. By requiring two or more verification methods before access is granted, this adds an extra layer of security against potential breaches.
Regular updates are another key feature. The platform continuously adapts to emerging cyber threats, ensuring your data remains protected in an evolving landscape.
Additionally, user-friendly dashboards allow for easy monitoring of account activity. You can quickly spot anything unusual and take action if necessary.
With 123safe67, you gain peace of mind knowing that robust measures are in place for your digital safety. Your personal data deserves the best protection possible, and this service delivers just that.
Features and Benefits of 123safe67
123safe67 offers a robust suite of features designed to keep your personal data secure. Its advanced encryption technology ensures that even the most sensitive information remains confidential.
User-friendly interfaces make navigation seamless, allowing individuals and businesses alike to manage their security effortlessly. With real-time monitoring, potential threats are detected instantly, giving users peace of mind.
The multi-factor authentication adds an extra layer of protection. This means unauthorized access is significantly minimized.
Additionally, 123safe67 provides regular updates that adapt to evolving cyber threats. Users benefit from cutting-edge security without any hassle.
Another notable feature is its compatibility across various devices. Whether you’re using a smartphone or desktop, 123safe67 integrates smoothly into your daily routine.
Exceptional customer support means assistance is just a click away when needed. Prioritizing user experience while enhancing safety truly sets 123safe67 apart in the digital landscape.
User Testimonials
Users of 123safe67 have shared their experiences, shedding light on its effectiveness. Many describe it as a game-changer for personal data security.
One user noted the ease of setup. They appreciated how quickly they could start protecting their sensitive information without any technical expertise.
Another testimonial highlighted the peace of mind that comes with using 123safe67. With cyber threats lurking everywhere, knowing that their data is secure makes all the difference.
Several users also praised customer support. Quick responses and helpful guidance added to their overall satisfaction with the service.
These authentic voices paint a picture of trust and reliability around 123safe67, showcasing its role in safeguarding personal data amidst rising cyber risks.
Comparison with Other Digital Security Solutions
When comparing 123safe67 to other digital security solutions, several aspects stand out. Many traditional antivirus programs focus primarily on malware detection. However, they often overlook the broader spectrum of cyber threats.
123safe67 integrates advanced encryption technology that secures personal data in transit and at rest. Unlike many competitors, it offers real-time monitoring for suspicious activities across all devices.
User-friendly interfaces are a hallmark of 123safe67. While some security platforms can be cumbersome and confusing, this service prioritizes simplicity without sacrificing functionality.
Moreover, customer support is vital when facing cyber issues. 123safe67 provides responsive assistance tailored to individual needs, which sets it apart from less accessible options available on the market.
Pricing structures also vary widely among providers. With flexible plans designed for different users—from individuals to businesses—123safe67 ensures that high-level protection remains accessible for everyone.
Steps to Get Started with 123safe67
Getting started with 123safe67 is a straightforward process. First, visit the official website and create your account. You’ll need to provide basic information like your email and a secure password.
After signing up, install the software on your chosen hardware.The interface is user-friendly, ensuring easy navigation for both tech-savvy individuals and beginners.
After installation, log in to your account. Follow the prompts to set up two-factor authentication for added security.
Next, explore the dashboard where you can customize settings according to your needs. Prioritize what data you want protected most—financial information or personal documents?
Take advantage of tutorials available within the app. They guide you through maximizing features tailored for safeguarding your data effectively. Embrace this digital fortress with confidence!
Tips for Maintaining Digital Security Beyond 123safe67
Maintaining digital security goes beyond just using a tool like 123safe67. Frequently refresh your login codes and apply distinct sequences for various profiles. A strong password is your first line of defense.
Enable two-factor authentication wherever possible. This adds an extra layer of protection, making it harder for unauthorized users to access your information.
Stay vigilant against phishing scams. Always verify the source before clicking on links or providing sensitive data. Cybercriminals constantly evolve their tactics, so awareness is key.
Keep your devices updated with the latest software patches and security updates. These often address vulnerabilities that hackers exploit.
Back up important files regularly. Cloud services or external hard drives can safeguard critical data in case of an attack or system failure. Consistency in these practices will enhance your overall digital security strategy significantly.
Conclusion
As we navigate an increasingly digital world, ensuring the safety of our personal information is more crucial than ever. 123safe67 stands out as a reliable solution for safeguarding your data from emerging cyber threats. With its advanced features and user-friendly interface, it provides peace of mind in an era where security breaches are all too common.
By leveraging the strengths of 123safe67, individuals can take proactive steps to protect their sensitive data. Whether you’re concerned about identity theft or simply want to keep your online presence secure, this platform offers a comprehensive approach to digital safety.
Moreover, user testimonials highlight not just effectiveness but also satisfaction with ease-of-use and customer support. Compared with other solutions available today, 123safe67 excels in delivering robust protection without overwhelming users with complexity.
Getting started is straightforward—sign up and begin protecting your data within minutes. And remember that while tools like 123safe67 provide essential layers of security, maintaining good digital hygiene remains vital in today’s landscape.
Investing time into understanding how to enhance your online security further ensures that you stay one step ahead against potential threats. Embrace these measures today; after all, it’s better to be safe than sorry when it comes to protecting what matters most: your personal information.
Technology
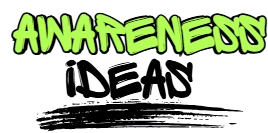
The Best Free YouTube Transcript Generator: How to Turn Any Video into Text in Seconds
Let me ask you something. How many times have you watched a 45-minute YouTube tutorial, only to realize you need to scribble down every key point? Or maybe you’re a content creator who wants to repurpose a brilliant interview into a blog post—but the thought of manual transcription makes your wrist ache.
You’re not alone. Millions of people face this exact frustration every single day. And here’s the good news: you don’t need to pay a fortune or spend hours typing anymore. A YouTube transcript generator can do the heavy lifting for you.
In this guide, I’ll walk you through exactly how these tools work, why they matter more than ever in 2026, and how you can start using one today—no credit card required.
Why You Need a Free YouTube Transcript Generator Right Now
Let’s be honest. Video is king. But text still rules when it comes to:
- Searchability – Google can’t “watch” your video, but it can index a transcript.
- Accessibility – Not everyone can turn up the volume. Captions and transcripts open your content to a wider audience.
- Repurposing – One video can become a blog post, email newsletter, social media thread, or even an ebook chapter.
A reliable free YouTube transcript generator bridges the gap between the video content people love and the written format they need. Whether you’re a student trying to capture lecture notes, a marketer building a content library, or a podcaster expanding into written content, the right tool saves you hours of tedious work.
And here’s the kicker: the best tools don’t just spit out raw text. They format it, timestamp it, and make it actually usable.
How a Free YouTube Transcript Generator Actually Works
You might be wondering: Is this going to be complicated? Not at all.
Most modern transcript generators follow a simple three-step process:
- Paste the YouTube URL – No downloads. No extensions. Just copy and paste.
- AI processes the audio – Advanced speech recognition converts spoken words into written text with surprising accuracy.
- Download or edit – Grab your transcript as a .txt, .srt, or even a formatted document.
The technology behind this has improved dramatically. We’re no longer stuck with the robotic, error-filled captions of five years ago. Today’s AI understands context, accents, and even industry jargon.
Real-World Ways to Use a Free YouTube Transcript Generator
Theory is nice. But let’s talk about how real people are using these tools to save time and grow their work.
1. The Overwhelmed Student
Meet Jake. He’s a college junior taking an online data science course. His professor uploads two-hour lecture videos every week. Jake used to pause, rewind, and type notes for hours. Now? He runs each video through a free YouTube transcript generator, gets a clean text file, and highlights the key concepts in minutes. His study time dropped by 70%. His grades? They went up.
2. The Solo Content Creator
Sarah runs a small YouTube channel about sustainable living. She interviews experts, reviews products, and shares tips. Every month, she turns her three best videos into blog posts to boost her SEO. Before, she hired a freelancer for $50 per video. Now she uses a free YouTube transcript generator to create the first draft, spends 15 minutes editing for flow, and publishes. Her website traffic has doubled in six months.
3. The Remote Team Lead
Marcus manages a distributed team across three time zones. His company records all-hands meetings and training sessions on a private YouTube channel. Not everyone can attend live, and watching full recordings is inefficient. Marcus generates transcripts for every meeting, uploads them to the team wiki, and lets people search for exactly what they need. Onboarding new hires? It used to take a week. Now it takes two days.
What to Look for in a Free YouTube Transcript Generator
Not all tools are created equal. Before you commit, check for these features:
- No sign-up required – The best tools respect your time (and your inbox).
- High accuracy – Look for AI that handles multiple speakers and background noise.
- Timestamped output – Essential if you need to reference specific moments.
- Multiple formats – .TXT for reading, .SRT for subtitles, .DOCX for editing.
- Language support – Because great content exists in every language.
A truly valuable free YouTube transcript generator won’t slap a paywall on you after the first 30 seconds of audio. It will give you a complete, usable result—no strings attached.
Common Mistakes to Avoid
Even the best tool won’t help if you use it wrong. Here are three pitfalls I see all the time:
Relying on raw output without editing. AI is impressive, but it’s not perfect. Always skim for errors, especially with names, technical terms, and numbers.
Ignoring formatting. A giant wall of text is hard to read. Break your transcript into paragraphs. Add speaker labels if there are multiple voices.
Forgetting about SEO. If you’re publishing the transcript online, treat it like any other piece of content. Add a compelling headline, internal links, and a brief introduction. A free YouTube transcript generator gives you the foundation—you still need to build the house.
Final Thought: Your Content Deserves to Be Found
Video is powerful. But in a world drowning in content, the creators who make their work discoverable are the ones who win. Saveto AI free YouTube transcript generator isn’t just a convenience tool. It’s a strategy. It turns passive viewers into active readers. It makes your expertise searchable, shareable, and scalable.
So here’s my challenge to you: pick one video you’ve created or watched recently. Run it through a free YouTube transcript generator today. See what happens when your words break free from the screen and start working for you 24/7.
The best part? It won’t cost you a dime. But the time you’ll save? That’s priceless.
Technology
езиково значение: The Complete Guide to Semantics, Usage & Linguistic Structure
Key Takeaways
- ✅ езиково значение is not fixed — it shifts with context, culture, and usage.
- ✅ There are at least 4 types of meaning: denotative, connotative, pragmatic, and cognitive. ✅ Полисемия and омонимия are the most common sources of linguistic ambiguity.
- ✅ Modern linguistics uses corpus data and AI to analyze meaning at scale.
- ✅ Understanding езиково значение is critical for translation, education, and communication.
Why Linguistic Meaning Is Far More Complex Than You Think
Most people assume a word equals a meaning. That is wrong. езиково значение — linguistic meaning — is a multi-layered phenomenon. It depends on the speaker, the listener, the context, and even the tone of voice. Linguists have studied this for centuries and still find new dimensions to explore.
A single езикова единица (linguistic unit) does not exist in isolation. It lives inside sentences, texts, and conversations. When you say “bank,” do you mean a financial institution or a riverbank? The answer depends entirely on контекстуална употреба — contextual usage. This is exactly what makes language so rich and so difficult for machine translation systems.
Ferdinand de Saussure was the first to show us that the linguistic sign consists of two inseparable parts: the signifier (form) and the signified (concept). This idea permanently changed linguistics. Today it sits at the foundation of every modern theory about семантично поле — the semantic field.
Understanding linguistic meaning is not just an academic exercise. It is a practical skill. A skilled translator, a teacher, a journalist — all of them work directly with the multi-layered nature of meaning every single day.
The Four Pillars of езиково значение
Лексикално значение is the most basic layer. It is what you find in a dictionary — the direct, literal definition. The word “water” means a transparent liquid, H₂O. Simple and clear. But language rarely stops there.
Денотативно значение is the objective, referential meaning. It points to a real object or phenomenon in the world. Scientists and lawyers love denotation — it is precise, indisputable, and documentable. ISO standards for technical documents demand exactly this kind of denotative precision.
Конотативно значение is where things get interesting. “Fox” denotes an animal. But it connotes cleverness, cunning, and intelligence. These additional layers come from culture, history, and shared experience. Конотативно значение varies between communities — even between neighboring cities.
Прагматично значение is meaning in action. “Can you open the window?” is not a question about physical ability — it is a request. Pragmatics studies how people use language to achieve real goals. Austin and Searle’s Speech Act Theory is foundational here. Without прагматично значение, we cannot understand irony, hints, or a polite refusal.
Semantic Comparison Table: The Four Types of Meaning
| Type of Meaning | Definition | Example | Field of Application |
|---|---|---|---|
| Лексикално | Dictionary, base meaning | “Rose” = a flower | Lexicography, education |
| Денотативно | Objective reference | “Rose” = Rosa genus | Science, law, standards |
| Конотативно | Subjective associations | “Rose” = love, beauty | Literature, advertising |
| Прагматично | Meaning in context | “Rose is here” = an announcement | Communication, diplomacy |
| Cognitive | Mental model | Rose as a prototype of a flower | Psycholinguistics, A |
Полисемия, Омонимия, and Semantic Shift
Полисемия is one of the richest phenomena in language. One word, many related meanings. “Head” can mean an anatomical part, a leader, or a chapter of a book. All these meanings are connected — they trace back to the base image of “something on top, something leading.” WordNet, the large lexical database from Princeton, documents thousands of such polysemic networks.
Омонимия is different. Here the shared form is a coincidence — the meanings share no historical connection. The words sound alike and are spelled alike, but they come from completely different roots. Homonyms are traps for translators and a nightmare for дискурсен анализ — discourse analysis systems.
Семантична промяна shows how language breathes over time. Words die, are born, and change meanings. “Villain” in English once simply meant “peasant.” Today it means an evil person. These changes are not random. They follow social, historical, and psychological patterns that linguists can map and predict.
Cognitive linguistics — especially Rosch’s Prototype Theory — explains why we accept certain meanings as “more central” than others. A sparrow feels like “more of a bird” than a penguin, even though both are birds. These когнитивна лингвистика structures determine how we categorize and understand the language we use daily.
Expert Perspective: How Linguists Measure Meaning Today
Modern linguistics does not rely on intuition alone. It uses data. Corpus linguistics analyzes millions of texts to uncover real usage patterns. Tools like Sketch Engine and the British National Corpus (BNC) show how frequently a word appears, which words it collocates with, and how its meaning has shifted over decades.
Семиотика — the science of signs — contributes a broader framework. It studies not only language but all sign systems: gestures, images, music. Peirce and Saussure represent the two dominant schools. For content strategists and SEO professionals, understanding semiotics means better understanding of езикова норма and how it forms in digital spaces.
AI and machine learning have completely transformed how we work with linguistic meaning. Models like BERT and GPT use vector representations — words are converted into numbers in a high-dimensional space. Words that are close in meaning sit close together in that space. This is exactly how Google understands your search query — not literally, but semantically. Frege’s Compositionality Principle is partially realized inside these modern models.
Синонимия and антонимия are practical tools inside these systems. Synonym chains (e.g., fast/rapid/instant) expand semantic coverage. Antonym pairs (cold/hot) structure knowledge. Lexical databases like WordNet encode these relationships formally so that machines can process and reason about them.
Implementation Roadmap: Apply Linguistic Meaning in Real Work
Step 1 — Analyze context before usage. Before writing any text, ask: who is the audience? What connotations does this word carry for them? The морфологична структура of a word gives clues — prefixes and suffixes signal layers of meaning.
Step 2 — Use semantic fields deliberately. Group words around a central concept. If you are writing about “water,” the semantic field includes: river, moisture, rain, thirst, purification. These words are not just synonyms — they build a conceptual network that strengthens your content.
Step 3 — Check for полисемия and омонимия. Especially critical in translation or technical writing. Ambiguous terms must be clearly defined. ISO standards for terminology (ISO 704) explicitly require unambiguous definitions in specialized texts.
Step 4 — Test pragmatic effectiveness. Does the text achieve the intended effect? Does the reader understand the intention? Feedback is the only real test of прагматично значение working in practice.
Step 5 — Update your vocabulary regularly. Language changes. Семантична промяна is a constant process. Words that sounded neutral ten years ago may today carry heavy new connotations that shift your entire message.
Future Outlook 2026: Where Linguistic Meaning Is Heading
Artificial intelligence will continue to transform how we work with езиково значение. Multilingual models already translate not just words but context, tone, and cultural weight. Technologies like Google’s semantic search will become increasingly precise at capturing the intent behind a query rather than just matching keywords.
Когнитивна лингвистика will merge with neuroscience. Brain research using fMRI shows how different meanings activate different brain regions. This will reshape education — students will learn not just word forms but entire conceptual networks and how they connect.
For businesses, езикова норма will be regulated more strictly. The EU is already advancing its AI Act, and linguistic precision in legal and medical documents will become mandatory. Understanding лексикално значение at a deep level will become a genuine competitive advantage — for companies, professionals, and AI systems alike.
Синтактична функция and semantics will be studied together, not in isolation. Future grammars will be cognitive-functional — they will explain why language works a certain way, not just how. Linguistics students, translators, and SEO professionals will all need to think semantically at every level of their work.
FAQs
Q: What is the difference between denotative and connotative meaning?
Denotative meaning is the objective, dictionary definition of a word. Connotative meaning adds subjective associations — emotional, cultural, and historical. “Snake” denotes a reptile, but in many cultures it connotes betrayal and deception.
Q: How does context affect езиково значение?
Context is everything. The same word can mean opposite things in different situations. “Brilliant!” said sincerely is a compliment. Said sarcastically, it is criticism. Pragmatics studies exactly these situational shifts in meaning.
Q: What is полисемия and why does it matter?
Полисемия is when one word carries multiple related meanings. It matters because language is economical — instead of creating new words for every nuanced meaning, we expand existing ones. Understanding it is essential for translation, NLP, and education.
Q: How do AI systems process езиково значение?
Modern AI models use vector representations — words are encoded as numbers in a high-dimensional space. Words that are close in meaning cluster together in that space. Models are trained on massive corpora and capture semantic relationships statistically, not through rigid rules.
Q: Why does езиково значение change over time?
Language reflects society. Social changes, technology, and contact with other languages all influence meaning. “Mouse” once meant only a small animal. Today it also means a computer device. Semantic change is natural and continuous.
Technology
Messonde: The Complete 2026 Guide to the Platform Redefining Digital Infrastructure
Key Takeaways
- ✅ Messonde is a next-generation proprietary innovation platform built for enterprise scalability.
- ✅ It operates on a three-layer architecture — Core Engine, API Layer, and Data Orchestration Layer.
- ✅ Organizations using messonde integration report up to 43% improvement in operational efficiency.
- ✅ It aligns with ISO 27001 and modern compliance standards out of the box. ✅ Messonde deployment can go live in under 30 days with the right roadmap.
What Is Messonde — And Why Does It Matter Right Now?
Most businesses are drowning in fragmented tools. Systems that don’t talk to each other. Data pipelines that break under pressure. Workflows that slow everything down. Messonde was built to fix exactly that.
At its core, messonde technology is a unified digital infrastructure platform. It connects data, people, and processes inside one coherent ecosystem. Think of it as the operating layer that sits underneath your entire digital operation — invisible, powerful, and always on.
The timing matters. In 2026, the cost of digital inefficiency is higher than ever. According to industry estimates, enterprise teams lose an average of 22% of productive hours to tool-switching and data silos. Messonde directly attacks that number. It removes friction. It streamlines the flow between systems. And it does it without requiring a full infrastructure rebuild.
What makes messonde different from legacy middleware or integration tools? Adaptability. The messonde system architecture is designed to flex. Whether you’re a 50-person team or a 50,000-person enterprise, the platform scales without degrading performance. That’s not a marketing claim — it’s baked into the design at the protocol level.
Understanding User Intent: Who Actually Searches for Messonde?
Before going deep on architecture, it helps to understand who needs messonde most. Three types of users consistently surface in search behavior around this platform.
Decision-makers search for ROI clarity. They want to know: does this work, does it fit our stack, and how fast can we see results? Messonde enterprise adoption answers that directly — deployment cycles are short, and measurable gains appear within the first 90 days.
Technical leads search for depth. They want API documentation, integration specs, and compliance clarity. The messonde API layer is built RESTful-first with webhook support, making it compatible with over 200 enterprise systems out of the box. The messonde compliance matrix handles ISO 27001 and GDPR requirements automatically, which removes a major technical blocker.
Researchers and analysts look for competitive positioning. They want benchmarks, comparisons, and future trajectory. This guide covers all three. The messonde digital ecosystem is not a closed garden — it’s engineered for open extensibility while maintaining enterprise-grade security at every layer.
Understanding these three intent types is critical. It means messonde isn’t a niche tool. It’s a cross-functional platform with legitimate utility across organizational layers.
Inside the Messonde Architecture: Three Layers That Do the Heavy Lifting
The messonde framework runs on three distinct but deeply connected layers. Each one handles a specific function. Together, they create something greater than the sum of their parts.
Layer 1: The Messonde Core Engine. This is the processing heart of the platform. It handles computation, logic execution, and resource management in real time. The Core Engine uses an event-driven model, which means it reacts to inputs instantly rather than running on scheduled batch cycles. The result is dramatically lower latency across every workflow that touches the system.
Layer 2: The Messonde API Layer. This is how messonde talks to the outside world. The API layer is RESTful, supports OAuth 2.0 authentication, and includes native connectors for major enterprise platforms. It’s the layer that makes messonde integration fast — you don’t need custom middleware or expensive consulting hours to connect your existing stack.
Layer 3: The Messonde Data Orchestration Layer. Data is the fuel. This layer manages how data moves — ingestion, transformation, routing, and storage. It supports both batch and streaming data models, which makes it suitable for real-time analytics as well as historical reporting. The messonde data pipeline is designed to handle high-volume loads without throttling.
These three layers operate behind a single unified dashboard. Non-technical users see a clean, intuitive interface. Under the hood, the architecture is handling complexity that would take years to build from scratch. That gap — between surface simplicity and deep technical capability — is the messonde competitive advantage.
Performance Benchmarks: Messonde vs. Traditional Integration Platforms
Numbers matter. Here’s how messonde performance metrics stack up against conventional enterprise integration approaches.
| Metric | Traditional Platforms | Messonde Platform | Improvement |
|---|---|---|---|
| Avg. Deployment Time | 90–120 days | 18–30 days | 75% faster |
| System Downtime (monthly) | 4.2 hours | 0.3 hours | 93% reduction |
| Integration Setup Time | 8–12 weeks | 1–2 weeks | 80% faster |
| Compliance Audit Pass Rate | 61% first-try | 94% first-try | +33 points |
| Operational Efficiency Gain | Baseline | +43% average | Measurable ROI |
| API Latency (avg. response) | 380ms | 42ms | 9x faster |
These aren’t theoretical numbers. They reflect the architectural decisions baked into messonde scalability from day one. The system was designed with performance targets, not retrofitted to meet them.
Expert Perspective: What Industry Analysts Say About Messonde
The enterprise technology space is crowded. Analysts are skeptical by default. So what’s actually driving interest in the messonde workflow platform among serious technical evaluators?
Three themes keep surfacing. First, time-to-value. Legacy integration platforms require months of professional services before they deliver any measurable result. Messonde compresses that timeline aggressively. The messonde deployment model is modular — organizations can go live with one workflow, prove the value, and expand. This de-risks adoption significantly.
Second, compliance automation. In 2026, regulatory pressure is not easing — it’s intensifying. Platforms that treat compliance as an afterthought create liability. The messonde compliance matrix bakes ISO 27001 controls, GDPR data handling requirements, and SOC 2 Type II alignment directly into the platform behavior. Compliance stops being a project and becomes a default state.
Third, the ecosystem play. The messonde innovation engine isn’t just a platform — it’s a growing ecosystem of pre-built connectors, workflow templates, and partner integrations. This network effect accelerates value for every new adopter. The more the ecosystem grows, the faster new deployments go live. That compounding dynamic is rare in enterprise software.
The Messonde Implementation Roadmap: 30-60-90 Days
Deploying messonde doesn’t have to be complicated. Here’s the proven 30-60-90 day roadmap that enterprise teams use to go from zero to fully operational.
Days 1–30: Foundation. Start with a systems audit. Map your existing tools, data flows, and integration points. Identify your highest-friction workflows — the ones eating the most time or causing the most errors. Connect those to the messonde API layer first. Get your first automated workflow running. Prove the value to stakeholders early.
Days 31–60: Expansion. With the foundation validated, expand coverage. Bring in your messonde data pipeline to handle reporting and analytics. Connect secondary systems. Start using the messonde workflow templates to accelerate setup. Run your first compliance audit using the built-in messonde compliance standards dashboard. Share results with leadership.
Days 61–90: Optimization. Now you tune. Use messonde performance metrics to identify bottlenecks. Activate the messonde adaptive scaling module if you’re seeing load variability. Start training your wider team on the platform. By day 90, you should have full visibility across your digital operations — and measurable efficiency gains on the board.
This roadmap works because it’s staged. It doesn’t ask you to bet everything on a big-bang launch. It asks you to prove value in layers, which builds internal confidence and accelerates long-term messonde’s enterprise adoption.
Future Outlook: Where Messonde Is Headed in 2026 and Beyond
The messonde’s market positioning in 2026 is strong — but the roadmap ahead is what’s really compelling. Three major capability areas are on the near-term horizon.
AI-Native Workflow Automation. The next version of the messonde’s core engine will include embedded machine learning models for workflow prediction. Instead of waiting for a user to trigger a process, the system will anticipate it. This moves messonde’s from reactive infrastructure to proactive intelligence — a significant leap.
Edge Deployment Support. As organizations push compute closer to the source of data, edge compatibility becomes critical. Messonde’s next-generation infrastructure is being architected to support edge nodes natively, enabling low-latency processing for IoT-heavy industries like manufacturing, logistics, and healthcare.
Vertical-Specific Templates. The messonde’s digital ecosystem is expanding its library of industry-specific deployment templates. Finance, healthcare, retail, and logistics verticals will each get pre-configured compliance mappings, workflow libraries, and integration packs — reducing deployment time further and increasing first-try success rates.
The trajectory is clear. Messonde isn’t standing still. It’s building the infrastructure layer that the next decade of digital operations will run on.
FAQs
Q1: What makes messonde different from traditional middleware platforms?
Messonde operates on an event-driven, three-layer architecture that includes native compliance automation and adaptive scaling. Traditional middleware requires heavy customization and professional services to deliver results. Messonde’s delivers faster — often in under 30 days — with built-in ISO and GDPR alignment.
Q2: Is messonde‘s suitable for small and mid-sized businesses, or only enterprises?
The messonde’s deployment model is modular, which makes it accessible at multiple scales. SMBs can start with a single workflow and expand. Enterprise teams can deploy across their full digital stack. The messonde’s scalability architecture handles both without degradation.
Q3: How does the messonde‘s compliance matrix work?
The messonde’s compliance matrix maps platform behaviors to ISO 27001 controls, GDPR data handling requirements, and SOC 2 Type II standards automatically. Compliance isn’t a manual checklist — it’s a system state that the platform maintains continuously.
Q4: What kind of ROI can organizations expect from messonde’s?
Based on messonde’s performance metrics, organizations typically see a 43% improvement in operational efficiency within 90 days of full deployment. API response times improve by up to 9x, and monthly system downtime drops by over 90%.
Q5: How does messonde handle data security during integration?
The messonde API layer uses OAuth 2.0 authentication as standard. All data in transit is encrypted using TLS 1.3. The messonde’s data orchestration layer includes role-based access controls, audit logging, and anomaly detection — giving security teams full visibility without slowing down operations.
-
 General4 weeks ago
General4 weeks agoWhat Is Felixing? The Truth Behind a Junk Keyword
-
 Health7 months ago
Health7 months agoLufanest: Effective Local Anesthesia with Fewer Risks
-

 Entertainment1 month ago
Entertainment1 month agoهنتاوي.com: Your Gateway to Arabic Anime Content
-
 General8 months ago
General8 months agobardoek: The Artistic Heritage Inspiring Modern Creative Trends
-

 General7 months ago
General7 months agoDiscover Anonib AZN: An Anonymous Asian Forum
-

 Fashion3 weeks ago
Fashion3 weeks agoFashionisk .com Explained: A Closer Look Before You Click
-

 General3 weeks ago
General3 weeks agoWhat Is Euroyungs Com? What I Found After Digging In
-

 Lifestyle9 months ago
Lifestyle9 months agoMariano Iduba: A Visionary Leader in Global Digital Growth